OTHER
Protecting Your Online Privacy on Social Media

Social media users worry about having little control over their personal information.
This is due to lack of faith that common communication methods, especially social media tools, are secure.
A survey by the Pew Research Center found that many adults know about government surveillance programs, and many Americans think the government should put more limits on advertisers. In addition, consumers don’t believe sharing personal data helps them much, but they’ll do it anyway to use free services.
1. Understand Online Privacy Protection Measures
Privacy usually means being alone without anyone watching or bothering you. But when you’re online, even by yourself, you’re still being watched and interrupted – by ads and companies tracking you.
Online privacy means controlling your personal information and what companies can see about your online activity. This includes deciding if and when companies can collect your data or track what you do online.
It matters for both your safety and how technology evolves. Poor privacy can lead to real harms like identity theft, stalking, and hacking. You probably don’t want robbers to know when you aren’t home. Or scammers using your details to pretend to be you and steal your money. So good privacy protections keep you safe.
Online privacy gives you control over your personal information. Without control, companies can use your identity however they want, like selling you things or stealing from you. Your privacy also impacts your family, friends, and colleagues. What you post publicly can affect how others see you. So protecting your privacy helps more than just you.
2. Maintain Control of Your Digital Footprint
A digital footprint is the trail of data you leave behind online. It includes things you actively share on social media, online profiles, and blogs. But it also consists of passive data collection – browsing history, purchase patterns, location data, and other information gathered by websites and apps, often without your knowledge.
Maintaining control over your records and information is crucial for protecting privacy online.
-
Data minimization involves only collecting the essential user data needed for services.
-
Extra unnecessary data poses privacy risks.
-
Records accessibility allows people to view, modify, and delete their stored data easily.
-
Data protection refers to encrypting information and transmitting data securely to prevent leaks.
-
Retention policies involve deleting user records after periods of inactivity since outdated data can create liabilities.
This passive data makes up a huge part of your digital footprint. And with billions of people online today, digital footprints have grown massive.
3. Know the Different Privacy Risks on Social Media

Your identity, accounts, and money can be at risk the more you share on social media. Here are some of the biggest social media privacy problems:
Hacking
Hackers can get clues to guess or trick you into giving your passwords by looking at the personal info you post.
Phishing Scams
Scammers send fake messages to get you to click on bad links or share info. 12% of clicks on phishing links are from social media.
Location Sharing
Location data on your posts and photos can let stalkers or thieves track you.
Identity Theft
Scammers only need some info from your profiles, like your address, to steal your identity.
Policy Changes
When social media sites change rules, sometimes private stuff accidentally becomes public.
Employers Checking
70% of employers look at candidates’ social media, and over half have found things that made them not hire someone.
Harassment
“Doxxing” is when hackers share your info to help others bother or threaten you.
Cyberbullying
Public accounts let bullies easily target you with mean messages.
Romance Scams
Scammers make fake profiles and trick you into relationships to get money or information.
Third-Party Apps
Logging in with social media can give your data to apps with bad security.
Malicious Links
Scammers send fake messages with bad links that can infect your device or steal your login info.
Data Collection
All your social media activity builds a “digital footprint” that advertisers buy to target your ads.
4. Follow Online Privacy Practices on Social Media
No one can eliminate their digital footprint today. However, following online privacy best practices greatly reduces risks and exposure from everyday digital activities.
Check Your Privacy Settings: Review each social media profile and ensure your privacy settings limit who can see your posts and information. Change any defaults to “Friends Only” or stricter options. Only share things publicly if you’re OK with anyone seeing them.
Share Less Personal Info: Be very selective about posting your address, phone number, birthday, relationship details, hometown, family name, and any other info an identity thief could use. Show some photos selectively. What seems harmless to share could give scammers clues to hack you.
Use a VPN: A VPN encrypts your internet traffic to keep what you do online private. It prevents websites from tracking your browsing history and hides your location. Many free and paid VPN options are available.
Review Third-Party App Permissions: Check what data access you have approved for any third-party apps connected to your social media accounts. Remove access to any unfamiliar apps or apps you no longer use.
Keep out Ad Targeting: Find the ad preference settings on social media sites and disable options for serving your targeted ads based on your activity or interests. This limits your digital footprint for advertisers.
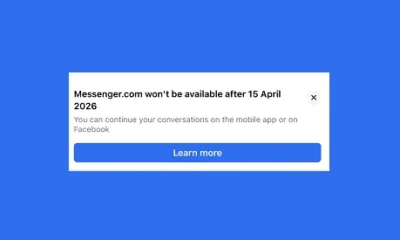
Delete Old Accounts: If you don’t use a social media platform anymore, delete or deactivate the account entirely if possible. This removes another place where outdated personal data could be exposed or hacked.
Think Before Posting Anything: Always use discretion when posting updates publicly or privately — even to close friends. Only share what would be harmless if publicly leaked.
5. Use Multi Factor Authentication and Keep up the with the Latest Updates

It’s important to use multi factor authentication to protect your passwords. Don’t forget to update your devices (apps, software, etc) and do not share sensitive information on social media. Following these basic precautions greatly reduces your risks from online tracking, hacking, fraud, and identity theft. Make privacy protection part of your regular social media routine. By taking responsibility for your social media presence and activities, you can improve safety for yourself and your loved ones.