NEWS
WordPress Facebook Feed Plugin Vulnerability Exposes 200,000+ Websites

Smash Balloon Social Post Feed, a WordPress plugin, was discovered to have a vulnerability that exposed the websites to allowing an attacker to upload malicious scripts. Security researchers at Jetpack discovered the vulnerability and notified the plugin publishers who patched it and released a fixed version, version 4.0.1. Versions prior to that one are vulnerable.
Smash Balloon Social Post Feed
Smash Balloon Social Post Feed WordPress plugin takes Facebook feeds and turns them into posts on a WordPress site.
The free version of the plugin is designed to display Facebook posts in a way that matches the look and feel of the site the Facebook content is republished on. The paid “pro” version also republishes images, videos and comments.
Stored Cross‑Site Scripting via Arbitrary Setting Update
A Stored Cross‑Site Scripting exploit (Stored XSS) is a form of cross site scripting vulnerability that allows a malicious attacker to upload and permanently store harmful scripts on the server itself.
Thee non-profit Open Web Application Security Project (OWASP) describes Stored XSS vulnerabilities:
“Stored attacks are those where the injected script is permanently stored on the target servers, such as in a database….
The victim then retrieves the malicious script from the server when it requests the stored information.”
Privilege and Nonce Checks Missing
The security warning published by Jetpack announced that the Smash Balloon Social Post Feed WordPress plugin had two security issues that caused it to become a security problem. Privilege and Nonce checks were missing.
XSS attacks can typically happen wherever there is a way to upload or enter something to a WordPress site. It can be through a form, in comments, wherever a user can enter data.
A WordPress plugin is supposed to shield the site by performing checks, among them a check for what level of privilege a user has (subscriber, editor, administrator).
Without a proper privilege check a user at the lowest level, like a subscriber, is able to carry out actions that normally require the highest levels of access, such as administrator level privileges.
A nonce is a one-time use security token that is meant to shield inputs from attacks.
The WordPress Nonce Documentation explains the value of nonces:
“If your theme allows users to submit data; be it in the Admin or the front-end; nonces can be used to verify a user intends to perform an action, and is instrumental in protecting against Cross-Site Request Forgery(CSRF).
An example is a WordPress site in which authorized users are allowed to upload videos.”
Jetpack identified a vulnerability in the Smash Balloon plugin that failed to perform the privilege and nonce checks, which opened up the site to attack.
Jetpack described how the vulnerability exposed websites:
“The wp_ajax_cff_save_settings AJAX action, which is responsible for updating the plugin’s inner settings, did not perform any privilege or nonce checks before doing so. This made it possible for any logged-in users to call this action and update any of the plugin’s settings.
Unfortunately, one of these settings, customJS, enables administrators to store custom JavaScript on their site’s posts and pages. Updating this setting is all it would’ve taken for a bad actor to store malicious scripts on the site.”
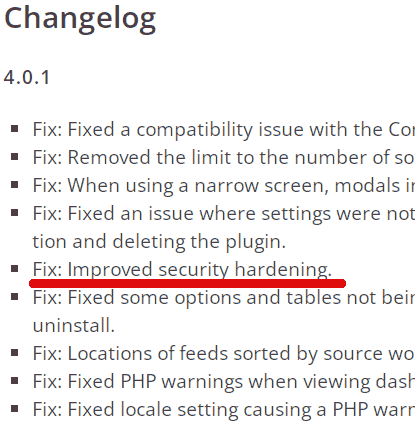
The Smash Balloon Social Post Feed WordPress plugin changelog, which records what every version update contains, properly notes that a security problem was fixed.
Not only is it responsible to fix vulnerabilities in a timely manner, which Smash Balloon did, but it’s also responsible to note it on the changelog, which Smash Balloon also did.
The changelog states:
“Fix: Improved security hardening.”
Screenshot of Smash Balloon Social Post Feed Changelog
Recommended Action
Smash Balloon Social Post Feed was recently patched to fix the Stored XSS attack that allows malicious scripts to be uploaded.
Jetpack recommends updating the Smash Balloon Social Post Feed to the latest version at this writing, which is version 4.0.1. Failure to do so may make a WordPress installation unsafe.
Citations
Jetpack Security Advisory
Security Issues Patched in Smash Balloon Social Post Feed Plugin
Stay in the loop with Entireweb
Get the latest updates delivered straight to your inbox. No spam - unsubscribe anytime.















You must be logged in to post a comment Login